Who Is at Risk of Identity Theft?
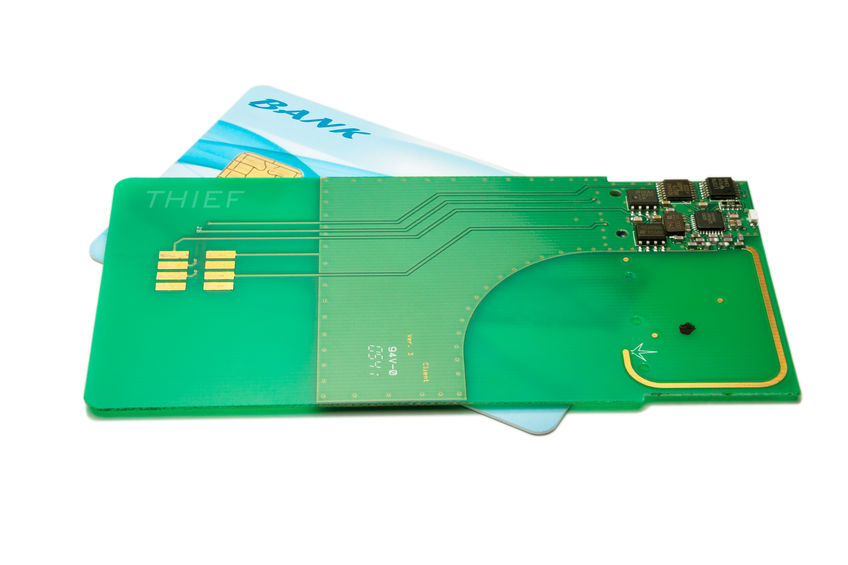
Identity theft can happen when your social security number, name and birthdate, and bank or credit card information is obtained. There are certain age groups that can be more at risk than others. The Consumer Sentinel Network Data Book 2019 published by the Federal Trade Commission January 2020 is a wealth of statistical information.